Some time ago, I received a new laptop, the HP Elitebook 845 G8. This is a 14″ laptop with an AMD CPU of the Renoir family, in my case an AMD Ryzen 7 PRO 5850U. As always, I run Debian GNU/Linux testing (currently Bookworm) on it. In this post, I will explain how to get all hardware working. This guide probably also works for other G8 Elitebooks, such as the Elitebook 835 G8 and Elitebook 855 G8, because they are all quite similar.
You can find detailed logs and reports of people running Linux on the Elitebook 845 G8 in the Hardware for Linux database.
Installation
I used a USB disk to boot the installer and a USB-C dock with an Ethernet interface to do a network installation. If you use the Debian installer with non-free firmware, you can also do the installation over wifi. I have not tried the current stable release Debian 11 Bullseye on this system. For best compatibility I strongly recommend testing because it has a more recent kernel and drivers.
Download the installation cd for Debian testing with non-free firmware: you need the file firmware-testing-amd64-netinst.iso.
Now we need to write it to a USB disk. Make sure there is no data on the drive you want to keep, because this process will completely wipe the disk.
To write the ISO image to a USB disk, Windows users can use the application Rufus, MacOS users can use Balena Etcher. If you are using Linux, you can dd the ISO image on your USB disk, or use a GUI like Fedora Media Writer.
Reboot the system and press F10 when the HP logo appears to load the BIOS/UEFI setup. Go to the Advanced page and select Boot Options. There make sure that USB Storage Boot is enabled. If you want to work with custom kernels, it can be handy to disable Secure Boot in Security – Secure Boot Configuration, but it’s not needed to install and use Debian.
Save the changes you made (if any) and reboot the system and press F9 at the HP logo to get the boot menu. In the boot menu, select your USB drive to start the Debian installer.
Enabling non-free repositories
We will need to configure the non-free repositories for apt because we need several firmware packages from non-free. Edit /etc/apt/sources.list and check whether any deb line has main contrib and non-free at the end. If not add it, and then run
# apt updateUpdating the BIOS/UEFI firmware
If you have a Windows installation, you can update the firmware from there, even before you install Linux. But you can also update the firmware without Windows. Follow the instructions in that blog post. It’s important to do this, not only because this gives you essential security fixes, but also bug fixes, some of which specifically for Linux compatibility.
Updating CPU firmware
Install the package amd64-microcode to ensure your AMD CPU is always running the latest microcode, which includes security fixes:
# apt-get install amd64-microcodeFlashing other firmware
The fwupd utility can download and install firmware from the LVFS. The firmware of the fingerprint reader of the Elitebook 845 G8, can be updated like this, and may be necessary to get the fingerprint reader working in Linux. First make sure fwupd is installed:
# apt install fwupd fwupd-amd64-signedNow update all available firemware:
# fwupdtool updateIf you have a HP USB-C Dock G5, then new firmware is also available in the LVFS, but it’s in the testing repository. To enable this repository, run this command:
# fwupdmgr enable-remote lvfs-testing Radeon Vega GPU
lspci identifies this GPU as
04:00.0 VGA compatible controller [0300]: Advanced Micro Devices, Inc. [AMD/ATI] Cezanne [1002:1638] (rev d1)First make sure the firmware is installed for the GPU. This is needed to get any hardware acceleration.
# apt install firmware-amd-graphicsThen make sure these packages are installed in order to get Vulkan, VA-API, VDPAU and OpenCL support:
# apt install mesa-va-drivers mesa-vulkan-drivers mesa-vdpau-drivers mesa-opencl-icdNow add this to /etc/environment so that it uses the correct VDPAU driver:
VDPAU_DRIVER=radeonsiIn order to get GStreamer based players to use VA-API, you need to install this package:
# apt install gstreamer1.0-vaapiAfter installing the firmware and editing /etc/environment you will need to reboot your system.
Unfortunately most video players and web browsers still don’t use VA-API hardware acceleration by default, but this needs to be configured manually. I will write a separate article about that later.
Realtek wifi adapter
The wifi adapter is a Realtek RTL8822CE according to lspci:
01:00.0 Network controller [0280]: Realtek Semiconductor Co., Ltd. RTL8822CE 802.11ac PCIe Wireless Network Adapter [10ec:c822]Install the firmware to get it working:
# apt install firmware-realtekThis laptop can also be delivered with an Intel AX200 Wi-Fi 6 adapter (which is actually a better option than this one from Realtek). If you have this one, you will need to install the firmware-iwlwifi package instead.
Smartcard reader
lsusb identifies this smartcard reader as an Alcor AU9540:
Bus 005 Device 004: ID 058f:9540 Alcor Micro Corp. AU9540 Smartcard ReaderNote that it only sees the smartcard reader when a card has been inserted.
You will need pscd with the CCID driver to use this smartcard reader:
# apt install pscsdFingerprint reader
The fingerprint reader can be seen like this in lsusb:
Bus 003 Device 003: ID 06cb:00df Synaptics, Inc. Make sure you have installed all firmware updates with fwupd and then you need to install these packages:
# apt install fprintd libpam-fprintdIn GNOME, under Settings – Users you can enable login on fingerprint and add your fingerprints.
Sound
lspci:
04:00.5 Multimedia controller: Advanced Micro Devices, Inc. [AMD] ACP/ACP3X/ACP6x Audio Coprocessor (rev 01)<br />04:00.6 Audio device: Advanced Micro Devices, Inc. [AMD] Family 17h/19h HD Audio ControllerSound is working out of the box. I recommend switching from Pulseaudio to Pipewire.
Webcam
lsusb:
Bus 001 Device 002: ID 0408:5348 Quanta Computer, Inc. HP HD CameraThe webcam works out of the box. Many applications will see the IR camera as a second camera.
Bluetooth
lsusb:
Bus 003 Device 002: ID 0bda:b00c Realtek Semiconductor Corp. 802.11ac WLAN AdapterIf you use lsusb -v you will see that this is actually the Bluetooth Radio adapter. It is combined with the wifi adapter, hence the confusion.
Suspend/resume
HP does not support S3 (traditional suspend-to-ram/standby) in its recent Elitebooks any more, but instead uses s0ix (s2idle/suspend-to-idle/modern standby). S2idle support for AMD CPU’s was only added in Linux 5.11 with the amd_pmc driver. I recommend a very recent kernel, because later kernel versions had bug fixes in this regard too. However suspend regressed in stable update 5.17.3 (and others), a bug which was fixed in 5.17.5. I’m using a custom-built 5.17.5 kernel, but a fixed kernel will appear soon in Debian.
If you have HP Drivelock enabled, then your system will fail to resume. Drivelock is a security feature which can be set up in the BIOS and requires you to enter a password when starting up the system in order to access the contents of the disk. When trying to resume the system, fans start running, the keyboard backlight reacts to key presses, but the screen remains blank, nothing is written to logs and also network does not come up. Apparently this is a bug in HP’s BIOS/UEFI firmware which can be worked around by adding iommu=pt to the kernel command line. To do so, edit /etc/default/grub and add this to the variable GRUB_CMDLINE_LINUX_DEFAULT. For example:
GRUB_CMDLINE_LINUX_DEFAULT="quiet iommu=pt"Then update the GRUB configuration:
# update-grubInstall isenkram to help install drivers when plugging in hardware
Isenkram is a utitliy which will show a message when you connect hardware to your system and extra software or firmware is available for that hardware.
# apt install isenkramEnabling trimming of the NVME SSD
Enable the fstrim timer to make sure the SSD is trimmed on regular intervals:
# systemctl enable --now fstrim.timerIncreasing battery time
Switch to AMD P-state driver
AMD developed the amd_pstate driver which was introduced in Linux 5.17. amd_pstate offers better performance per Watt than acpi-cpufreq
/etc/modprobe.d/acpi-cpufreq-blacklist.conf
blacklist acpi-cpufreq/etc/modules-load.d/amd-pstate.conf
amd_pstateIf you are using Linux 6.3 you don’t need to do this, but you will have to add to the the GRUB_CMDLINE_LINUX_DEFAULT options in /etc/default/grub.conf:
amd_pstate=activeand run update-grub.
Set up TLP
TLP is a tool which optimizes power consumption of your system in order to increase battery time. TLP also has an options Radio Device Wizard, which I will use here to automatically disable wifi when the system is connected via an Ethernet cable.
# apt install tlp tlp-rdwConfigure the Radio Device Wizard by creating the file /etc/tlp.d/10-tlp-rdw.conf:
# tlp-rdw - Parameters for the radio device wizard
# Possible devices: bluetooth, wifi, wwan.
# Separate multiple radio devices with spaces.
# Default: <none> (for all parameters below)
DEVICES_TO_DISABLE_ON_LAN_CONNECT="wifi wwan"
DEVICES_TO_DISABLE_ON_WIFI_CONNECT="wwan"
DEVICES_TO_DISABLE_ON_WWAN_CONNECT="wifi"
# Radio devices to enable on disconnect.
DEVICES_TO_ENABLE_ON_LAN_DISCONNECT="wifi wwan"
DEVICES_TO_ENABLE_ON_WIFI_DISCONNECT=""
DEVICES_TO_ENABLE_ON_WWAN_DISCONNECT=""
# Radio devices to enable/disable when docked.
DEVICES_TO_ENABLE_ON_DOCK=""
DEVICES_TO_DISABLE_ON_DOCK=""
# Radio devices to enable/disable when undocked.
DEVICES_TO_ENABLE_ON_UNDOCK="wifi"
DEVICES_TO_DISABLE_ON_UNDOCK=""To enable best ASPM power saving features when on battery, create /etc/tlp.d/20-aspm.conf:
PCIE_ASPM_ON_AC=default
PCIE_ASPM_ON_BAT=powersupersaveYou will also need to edit /etc/default/grub file to add pcie_aspm=force to the Linux command line, for example
GRUB_CMDLINE_LINUX_DEFAULT="quiet iommu=pt pcie_aspm=force"And run update-grub to update the GRUB configuration.
Disable Bluetooth and wifi when on battery and they are not in use by creating /etc/tlp.d/30-disable-devices-on-battery.conf:
DEVICES_TO_DISABLE_ON_BAT_NOT_IN_USE="bluetooth nfc wifi wwan"Submitting your system to the Linux Hardware database
The Linux Hardware database is a useful tool where users searching for hardware, can check the compatibility of systems with Linux. I recommend running this tool on all your Linux systems. After submission, you will get a link where you can view the data and indicate whether all hardware works and which work-arounds you had to apply. Click on the Review button on the page to do so.
# apt install hw-probe
# hwprobe --all --uploadConclusion
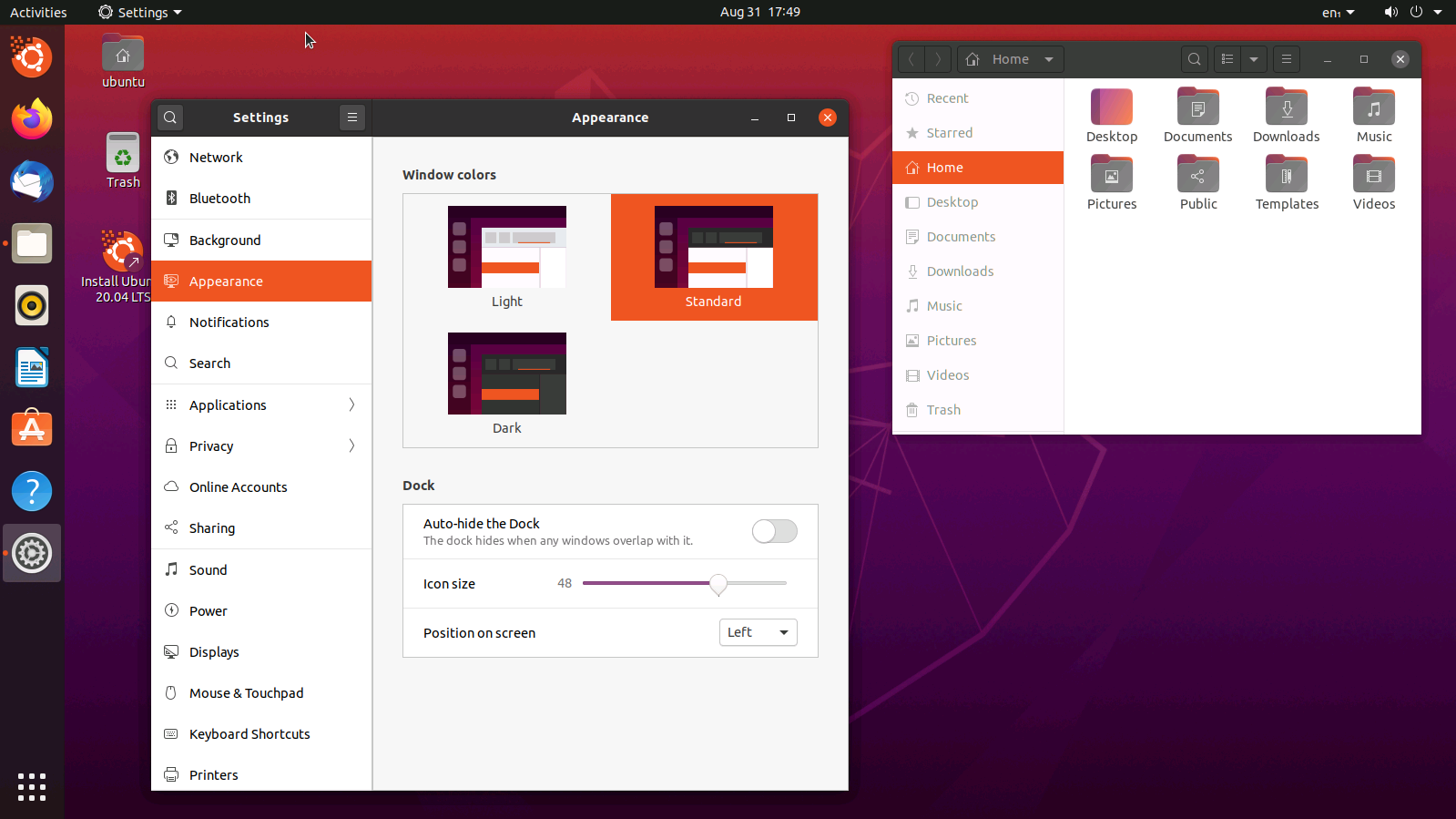
Actually Linux compatibility of the HP Elitebook 845 is actually in good shape. It’s not perfect, but all hardware can be made to work. On distros like Ubuntu, which install non-free firmware by default, it should even be easier to make everything work. Still HP lags behind Dell and Lenovo in Linux support, because they don’t make it possible to flash the BIOS/UEFI firmware using fwupd, while all recent Dell and Lenovo business laptops have their firmware available in the LVFS. Also the problem that iommu=pt needs to be used to successfully resume the laptop when Drivelock is enabled, is a problem that HP should address in a BIOS update.